Configuring AD FS SAML 2.0 Integration involves coordinated steps between the AD FS machine and YAROOMS.
Important: AD FS SAML can be integrated with YAROOMS only if all LDAP accounts meant to use the integration have valid email addresses attached.
Step 1: Generate Token Signing Certificate and Obtain AD FS URL
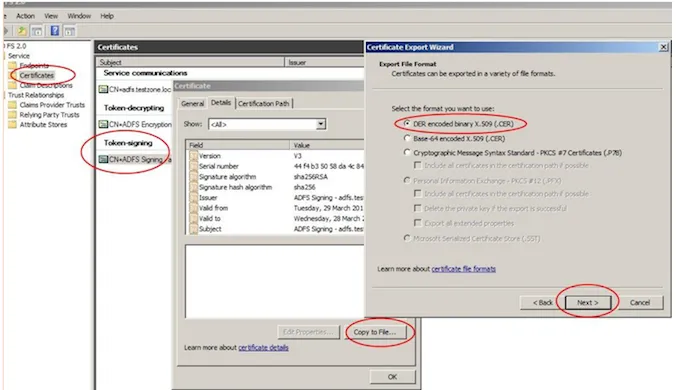
On the AD FS machine, navigate to Administrative Tools → AD FS Management. Expand Services in the left pane and click Certificates. Double-click the Token Signing certificate, then select the Details tab.
Click Copy to File and save the certificate in DER format. Convert the file to PEM format using a tool like OpenSSL or an online converter (SSLShopper, RapidSSLOnline, etc.). Store the resulting hash for later use.
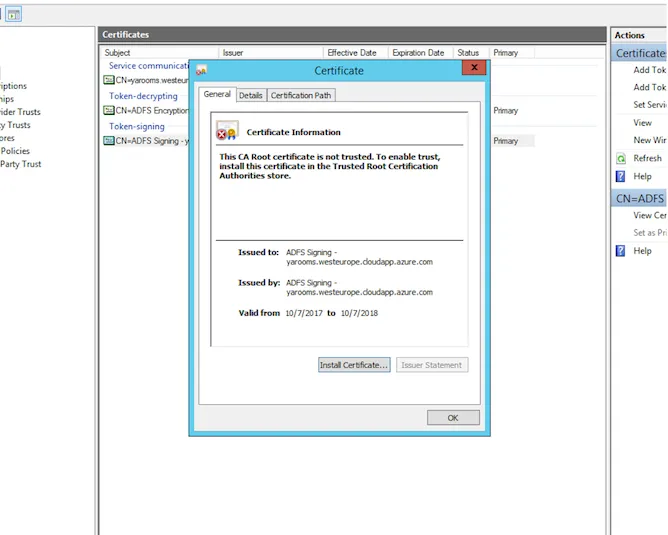
In the certificate’s General tab, locate the external server URL under “Issued to” and “Issued by” fields. Store this value (example: https://yarooms.westeurope.cloudapp.azure.com).
Step 2: Get the Issuer URL
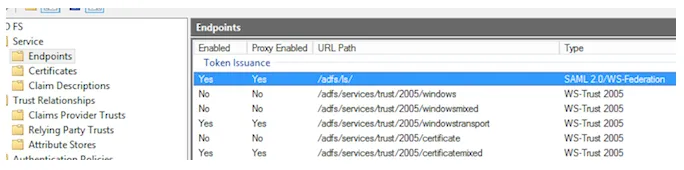
Close the certificate window and click Services → Endpoints. Scroll to the Metadata section and locate the item with Type: Federation Metadata.
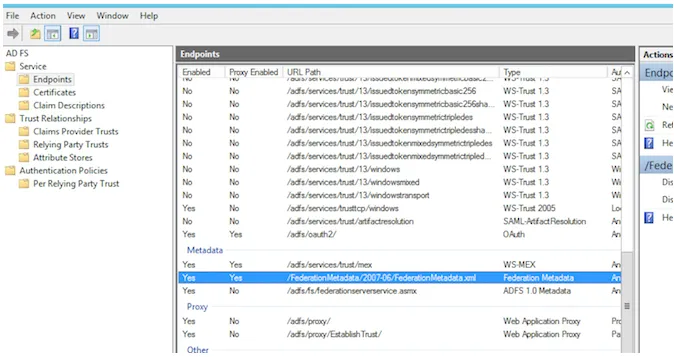
Combine the URL Path with the server URL. Example result:
https://yarooms.westeurope.cloudapp.azure.com/FederationMetadata/2007-06/FederationMetadata.xml
Access this link and open the XML file.
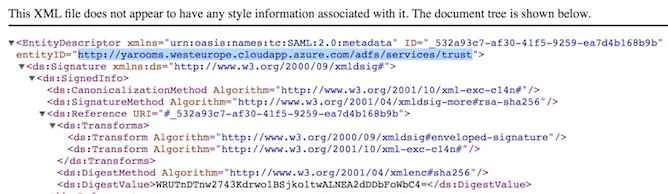
Look for the entityID property value—this is the Issuer URL. Example:
https://yarooms.westeurope.cloudapp.azure.com/adfs/services/trust
Step 3: Get the SAML Endpoint
Return to the Endpoints list and scroll to the Token Issuance section. Find the item with Type: SAML 2.0/WS-Federation and copy the value. Combine it with the server URL from Step 1.
Example result:
https://yarooms.westeurope.cloudapp.azure.com/adfs/ls/
Note: The trailing slash is mandatory.
Step 4: Set Up Trust Relationship on AD FS
Click Trust Relationships → Relying Party Trusts, then click Add Relying Party Trust. Follow these wizard steps:
- Data Source: Enter data about the relying party manually
- Display Name: Specify a name (e.g., YAROOMS SAML)
- Profile: AD FS Profile
- Configure Certificate: Leave blank
- Configure URL: Enable “SAML 2.0 Web SSO Protocol” and enter a placeholder URL (your YAROOMS domain)
- Configure Identifiers: Enter a placeholder URL and click Add
- Multi-factor Authentication: Check “I do not want to configure multi-factor…”
- Issuance Authorization Rules: Select “Permit all users to access this relying party”
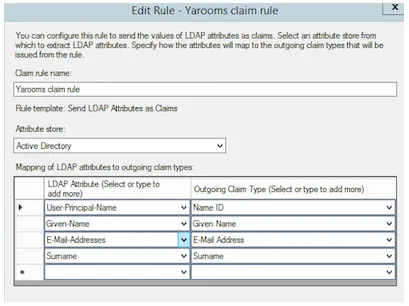
Complete the wizard and open the Edit Claim Rules Dialog. In the Issuance Transform Rules tab, click Add Rule.
- Rule Type: Send LDAP Attributes as Claims
- Claim rule name: Provide a descriptive name
- Attribute Store: Active Directory
- LDAP Attribute Mappings:
- User-Principal-Name → Name ID
- Given-Name → Given Name
- E-Mail-Addresses → E-Mail Address
- Surname → Surname
Step 5: Configure SAML 2.0 in YAROOMS
Log in as administrator to YAROOMS and navigate to Integrations → SAML 2.0 Authentication. In the Connection tab, populate the form:
- Identity Provider: Type “AD FS” (this label appears on the login page)
- Issuer URL: From Step 2
- SAML Endpoint: From Step 3
- X.509 Certificate: The PEM-formatted hash from Step 1 (Begin/End Certificate comments are optional)

- Name ID Format: Select unspecified
- Attributes Mapping:
- Map First Name to
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/givenname - Map Last Name to
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/surname - Map Email Address to
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress
- Map First Name to

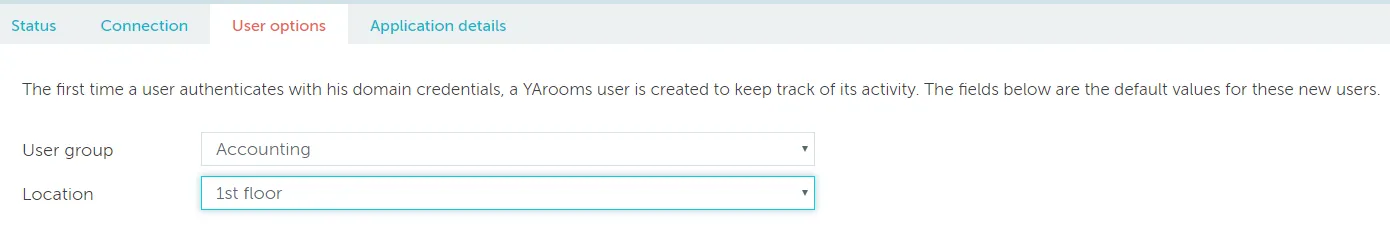
Save options and navigate to the User options tab. Set default group and location for new users created from Identity Provider data.
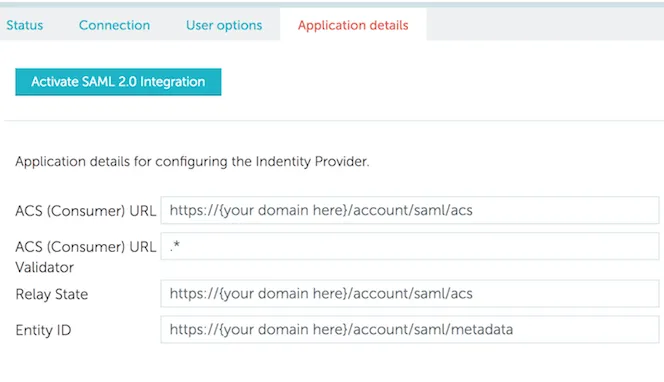
Save and navigate to the Application details tab. Activate SAML Integration. The values displayed are placeholders dependent on your YAROOMS account.
Step 6: Complete Trust Relationship Settings on AD FS
Return to the AD FS machine and edit the Relying Party Trust.
- Advanced tab: Set Secure hash algorithm to SHA1
- Identifiers tab: Add a Relying party identifier using the Entity ID URL from YAROOMS Application details

- Endpoints tab: Click Add SAML

Configure the new endpoint:
- Endpoint type: SAML Assertion Consumer
- Binding: POST
- Trusted URL: The ACS (Consumer) URL from YAROOMS Application details
Note: User provisioning and assignment in AD FS are organization-specific and not covered in this tutorial. You are responsible for configuring these settings and assigning user access to the YAROOMS application.